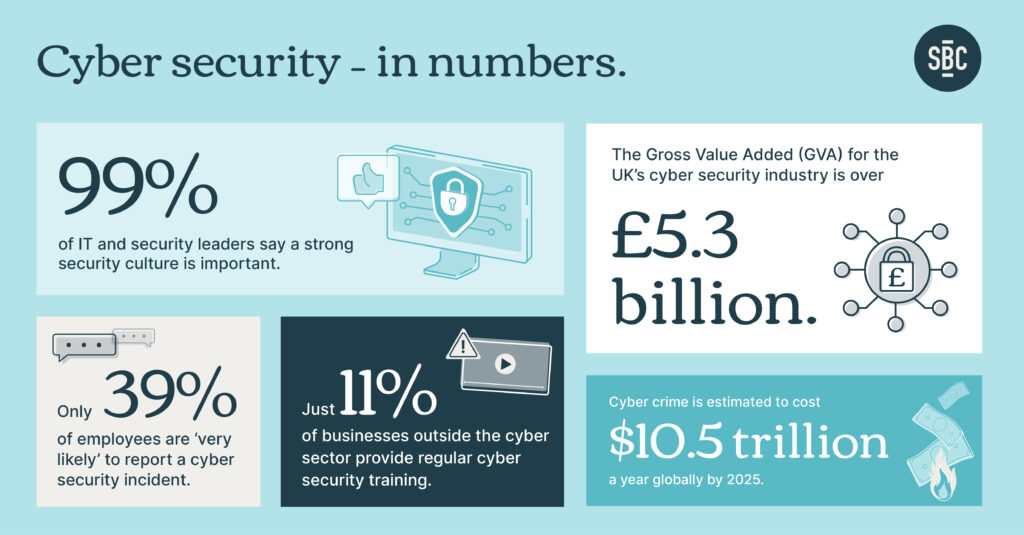
Cyber security is big business. Over the next three years, the UK government alone is spending a hefty £2.6 billion on it.
Dig around, and you’ll see why. More than 80% of UK firms have experienced an attack and the average cost of a security breach runs into the millions. Added to this, the UK govt reports that 697,000 businesses have a ‘basic skills gap’ when it comes to security and 451,000 have ‘more advanced skills gaps’.
As for cyber security training? The figures don’t get much better. Half of learners think that cyber security training is ‘ineffective’. And industry trainers may want to look away now: a paltry 28% of learners feel like security training is ‘engaging’, and only 36% say they ‘pay full attention’ during it.
Which, all in all, leaves us in a bit of a pickle.
But, when you think about it, most security breaches involve someone doing something. They click on a link. Open a message. Type in personal details. Some sort of behaviour.
Surely, then, cyber security training to combat that should include behavioural effects? And wouldn’t these same effects keep those 72% of unengaged learners upbeat, animated and, well, actually learning.
We think so. That’s why when we conduct data and cyber security training we make sure we pack it with bags of techniques borrowed from behavioural science. These are tried and tested. Discovered by scientists and those in the field, used in products that we’ve created around cyber and IT security awareness, and loved by learners.
Here are just a handful.
Fluency Effects
If it’s easy to read, it’s easy to do, pretty, good, and true. Or so say academics Song and Schwartz. Making things simpler and more readable makes them more memorable and believable. Think: ‘Hands, Face, Space.’ (Or, if you can bear it, ‘Live, Laugh, Love’.)
That’s why we strip key cyber security considerations down to their bare bones. We make sure they’re easy to read, understand, and act on. And we’ll reserve more heavy-duty, in-depth guidance for other assets and brochures (yet still keep it as readable and succinct as possible).
Chunking
How do you best digest huge, unwieldy wodges of information – you know the ones, those sprawling, never-ending walls of information that just go on and on and none of it goes in, not really, because there’s so much of it and the main points are all tangled up in a jumble of words, and, well, really, come on, how do you digest these huge, unwieldy wodges of cyber security information?
You digest them by breaking them down.
Into bite-sized chunks.
That’s how.
‘Chunking’ information aids short-term memory and helps process and cope with that information so much better.
So, in one of our data guidance programmes, we unified and divided material in order to conquer. We put all the information learners would need in a core, animated script. But we also split this information into various explainers and assets, so it wouldn’t appear too intimidating for our audience.
The S p a c i n g Effect
Learning doesn’t happen overnight. It’s iterative and cumulative.
That’s especially true when you’re not fully paying attention to what’s being presented because you are – like the UK government agencies we’ve done training for – busy helping run a country.
So, we spread cyber security messages out. On a campaign around spear-phishing that SBC created, for example, we drip-fed the information over time, across different media. This meant that people could more gradually internalise the risks – and how to avoid them.
The Generation Effect
We learn best not by listening or reading, but by trying ideas out for ourselves.
We could tell you how to perfect your one-handed backhand right here in words. But, let’s face it, until you get out there and start spraying your racket around, you won’t know if you’re going to become the next Roger Federer. (Spoiler alert: it’s unlikely.)
So cyber security training campaigns we run will typically involve plenty of quizzes and gamified elements. This gives learners the chance to interact and learn for themselves, rather than just sitting there absorbing slide after slide. An added bonus? Trying out something for yourself involves healthy degrees of autonomy – added catnip for learners.
Ego, Status and Desirability Bias
We like to present ourselves in the most positive light we can. It’s part of the reason we buy brands like Apple, Patagonia and Oatly – brands we feel represent what we want to convey about ourselves to the world.
To tap into this, our spear-phishing campaign’s hook was: ‘Don’t take the bait!’
Because none of us want to be the country bumpkin who falls for somebody’s cheap trick. The slogan appealed to people’s egos. The idea of succumbing to a spear-phishing email feels like something only a sucker would do.
Don’t want to be that sucker? Pay attention. Make sure you know the risks.
Zeigarnik Effect
Ever had that uncomfortable feeling of having an incomplete task hanging over you? Pretty draining, isn’t it?
Lithuanian psychology student Bluma Zeigarnik discovered in 1922 that our minds are often quick to forget about finished tasks but unfinished ones weigh us down.
Bluma is one reason we’ll include a progress bar in our training modules. This gives learners up-to-the-minute info on how far they have come and offers a little extra mental motivation to keep going and complete courses.
Picture Superiority Effect
As behavioural communications devotees, we’re big believers in the power of words. But we also appreciate that a picture can speak a thousand of them.
In a cyber security training campaign for that same UK government agency, we housed everything in a combination-lock graphic. A way of bringing information together in one place – while showcasing that the guidance was connected, unified and secure.
The picture superiority effect only really works when images are related to the content. In this instance, the lock image was (ahem) key. We wouldn’t have illustrated the serious business of data guidance with pictures of, say, multi-coloured horses. (Although perhaps we would if we’d made them Trojan horses with rainbow saddles – but, well, you get the picture.)